Identity Crisis: How many Online Identities should you have?
UOSM2033 Topic 2: Discuss the arguments for and against having more than one online identity
Identities & Personae
As the internet gets older, social media develops and the way we use the internet changes, the pressure on users to form strong online identities becomes greater and greater. From this added pressure arises the question of whether to have one large identity with a strong sense of brand or multiple identities that are suited for their own purposes.
Before we can discuss this, though, we must understand what exactly we mean by online identity. In their first tutorial on Online Identity, The Internet Society describes it as:
“the sum of your characteristics and interactions”
Or, the way in which you are viewed by others. Of course, every person you encounter (or, indeed, organisation, website or tracking software) will view different habits and characteristics that you display, and each builds up a slightly different image of you; these are referred to by The Internet Society as ‘Partial Identities’.
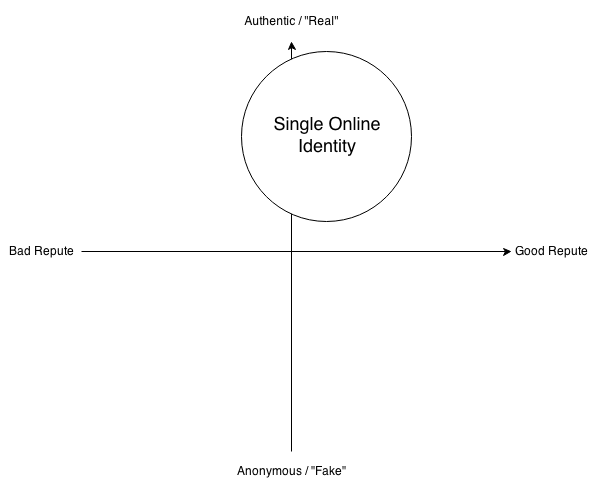
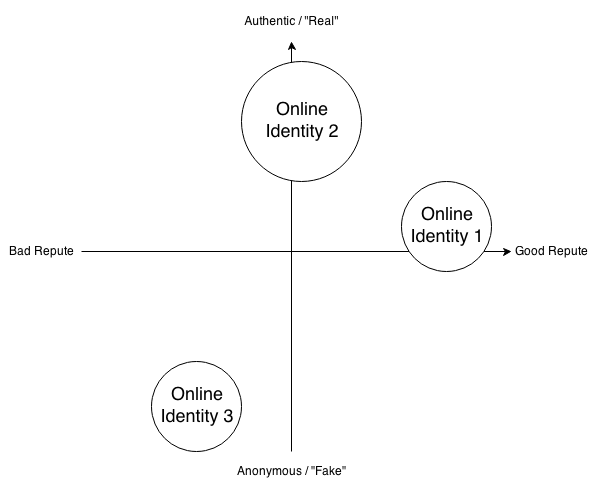
However, this variation is not useful when discussing the issue of multiple identities; rather, the cumulative identity is more important to consider. This cumulative identity becomes intrinsically linked to your persona (the character that you project to the internet) and it is this persona/cumulative identity duality that this question more specifically refers to. As such, it becomes obvious that if one projects a single persona, they will end up with one cumulative identity (Fig. 1), whereas if they have separate personae, each persona will have its own cumulative identity (Fig. 2):

Fig. 1: A single Persona resulting in a single Identity constructed around it, from the perspectives of a large variety of users. The diagram shows only three Partial Identities (and users behind them) that make up the single Identity, but in reality there could be hundreds, thousands, millions or even billions of Partial Identities that construct the single Cumulative Identity.

Fig. 2: Multiple Personae resulting in multiple Identities, each constructed from the perspectives of separate users, often grouped by relationship to the user. Please note that each Identity is constructed of multiple Partial Identities that are not shown on the diagram for simplicity’s sake.
Authenticity & Reputation
When examining the properties of identities, two are particularly relevant to the issue of multiple identities. In her Guardian article, Aleks Krotoski identifies that, in an era of Social Networking, where anonymous message boards like 4Chan are no longer the central social hubs of the internet, the authenticity of one’s Identity is coming under closer and closer scrutiny. Meanwhile, in Jonathon Zittrain’s blog post, he identifies reputation as one of the most important Identity Properties, and whilst he suggests that “Reputation Bankruptcy” might be possible in the future, we are not yet at that stage.
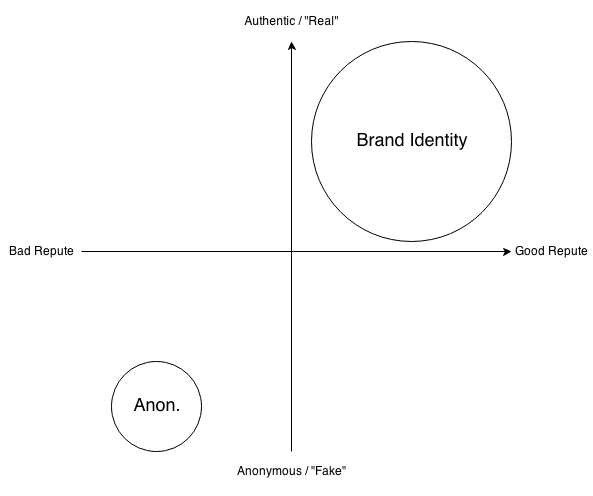
Putting these ideas into a chart allows us to identify four rough quadrants (Fig . 3):
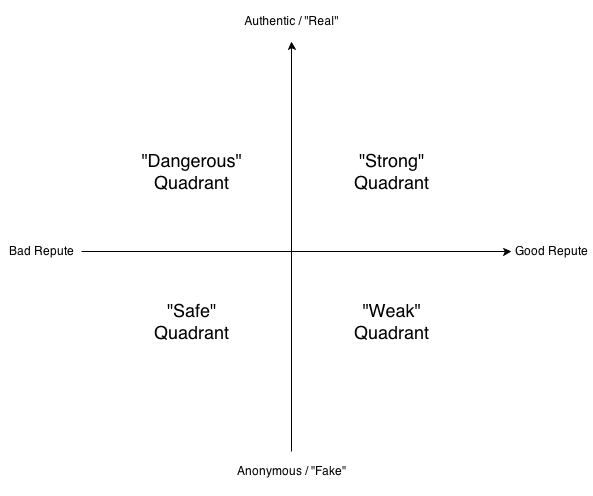
Fig. 3: Identifying Quadrants on a graph of “Authenticity” against “Reputation”. Whilst ‘Authentic’ and ‘Anonymous’ are not exact opposites, I felt that the two concepts are close enough that it most useful to place them at opposite ends of the same axis, rather than confuse the diagram with a third axis.
The four quadrants, whilst not entirely distinct from one another, are worth examining:
- “Dangerous”: So called because it involves a somewhat real or authentic aspect of yourself being connected to negative standing – giving yourself a “bad name”. Whilst for most people, this quadrant should be avoided, for some personae that thrive on being controversial or the “bad boy”, it can be invaluable.
- “Safe”: In this quadrant, anonymity protects the individual from negative associations from potentially contentious opinions or actions, from rants about bosses and co-workers to engaging in taboo activities.
- “Strong”: Where one should usually be aiming for when constructing a brand, this quadrant means that positive actions you engage in then reflect back onto your non-digital identity, creating opportunities for yourself.
- “Weak”: An anonymous identity that stands in good repute will not usually reflect back on the user’s non-digital life, though some people have based entire careers on being an anonymous good citizen.
It is obvious, then, that all Quadrants have their uses, but the “Strong” and “Safe” Quadrants are the most useful for the majority of users. Let us examine how the earlier figures could potentially map onto this:
The problems with Fig. 4 are instantly apparent: all actions one takes online come under the same identity, both good and bad. There are many reported instances of “oversharing” in the media, with workers regularly being fired for contentious comments made on Facebook (See Fig. 5).
Fig. 5: Google News search for “Fired for Facebook Post”, accessed on 26th October 2014. It should be noted that these are merely the most high profile cases, occurring around this date, and other instances go unnoticed by the media.
Fig. 6 is perhaps more representative of most users’ identities. Whilst at first glance, it appears to have similar problems to Fig. 4, many would use Identity 2 as a “private” identity, away from prying eyes, whilst maintaining a very corporate, business oriented Identity (1) and engaging in anonymous activity elsewhere (3). In this respect, multiple identities instantly seems far safer in terms of reputation. However, it it is worth remembering that privacy is limited – one need only examine the case of the recent case of Jennifer Lawrence’s leaked nude pictures to see that data on the internet is never entirely safe and is never completely lost – even in the cloud. A refined version of this graph where Identity 2 is made to have an entirely “good” reputation, shifting it to the right, would be an improvement, but there is a more pressing issue with this option.
An Ideal
It is obvious, then, that maintaining only one identity online is extremely risky, unless one acts in an entirely perfect manner, and few can claim that. However, whilst Fig. 6 has its own security issues, the biggest problem with it is that it actually achieves very little outside of the online world. With Identity 2 being private and Identity 1 being somewhat weak, impersonal and inauthentic, it opens up very few opportunities for the user. Indeed, if both Identity 1 and 2 are of good reputation, why separate them? It would be far stronger to construct a single Branded Identity, as this video from jetsetshow recommends:
Building a Brand is something that, for an artist such as myself (a composer) whose personality and engagement with audiences is key to their success, is vital. Since starting this module, I have been focusing my online activity into forming a Brand; using the same usernames and handles (MistmanX) is something I have always done, but using a common theme across multiple accounts and adding greater connectivity between them through about.me has been the start of what I hope to be a more successful online identity (See Fig.7).
Fig. 7: A selection of my profiles on the internet, using the same avatar and background images. Top Left: Facebook Top Right: Twitter Bottom: About.me
The brand should be, however, as the video states, “professional even when you’re being personal”. Forming a brand identity whilst also using anonymous identities for “under the radar” activities might therefore be considered an ultimate ideal, occupying only the “Strong” and “Safe” quadrants. Fig. 8 provides a graphic illustration:
This sort of approach has been adopted by many, including Devin Townsend on Twitter, who is very open about his emotions and activities but makes sure that what he shares is related to his music, making him very relatable. His regular interactions with fans on the site furthers his popularity, often being considered the darling of many online metalhead communities. Any other actions he takes online can in no way be related to him. His online identity therefore ends up being exceedingly authentic whilst remaining professional and in good repute.
For me, personally, my brand identity still has some way to go. Many of the accounts I have contain very little content, and some of my accounts with the MistmanX username are related to things that I do not want to be associated with my identity in the future (as I have owned some of these accounts for a very long time). However, what I have achieved is a strong infrastructure for a single identity brand that I can carry forward, as I aim towards the ideal of Figure 8.
References & Bibliography
Arthur, C. (2014). Naked celebrity hack: security experts focus on iCloud backup theory. The Guardian.
Costa, C. and Torres, R. (2011). To be or not to be, the importance of Digital Identity in the networked society. Educação, Formação & Tecnologias, University of Salford.
Diaz, Z. (2010). 7 Steps To Building Your Online Identity. Epic Fu on jetsetshow.
The Internet Society (Accessed 2014). Manage Your Identity. The Internet Society.
Krotoski, A. (2012). Online identity: is authenticity or anonymity more important? The Guardian.
Townsend, D. (Accessed 2014). Devin Townsend (@dvntownsend). Twitter.
Vincent, J. (2014) Google removes links to websites hosting Jennifer Lawrence stolen nudes. The Independent.
Warburton, S. et al. (2010). Rhizome – Digital Identity Matters. King’s College, London.
Zittrain, J. (2010). Reputation Bankruptcy. The Future of the Internet and How to Stop It, Harvard Law School.